What Is Black Hat USA 2026?
Black Hat USA 2026 is the premier cybersecurity conference, returning to the Mandalay Bay Convention Center in Las Vegas, NV from August 1–6, 2026. The event brings together security researchers, practitioners, and solution providers for six days of hands-on training, cutting-edge research presentations, and live tool demonstrations.
Now in its latest edition, Black Hat USA remains the industry's most respected platform for disclosing vulnerabilities, sharing offensive and defensive research, and building professional connections. Whether you specialize in exploit development, cloud security, or malware analysis, this event delivers actionable intelligence you can apply immediately.
Why You Should Attend?
Black Hat USA is where the cybersecurity industry sets its agenda for the year ahead. The Briefings track features peer-reviewed research on the latest risks, trends, and attack techniques — vetted by a review board that includes Lidia Giuliano, Jason Haddix, Window Snyder, and Anant Shrivastava.
The Trainings program offers four full days of intensive, expert-led courses covering ethical hacking, exploitation techniques, malware analysis, and cloud security. These sessions are taught by globally recognized practitioners and reviewed by a dedicated board including Daniel Cuthbert, Ping Look, Maria Markstedter, and Jonathan Squire.
New for 2026: The Business Hall now opens on Tuesday afternoon, giving attendees an extra half-day of networking, product demos, and face time with hundreds of solution providers. This change directly addresses attendee feedback requesting more time to explore the vendor floor.
Who Should Attend?
Black Hat USA 2026 is built for technical professionals across the cybersecurity spectrum:
- Penetration testers and red teamers looking to sharpen their offensive skills through hands-on Trainings
- Security engineers and architects seeking the latest defensive research and tooling
- CISOs and security leaders evaluating vendors, strategies, and emerging threats
- Threat intelligence analysts tracking new attack vectors and malware families
- Developers and DevSecOps practitioners focused on building secure systems from the ground up
- Students and early-career professionals aiming to break into the cybersecurity field
If your work involves protecting systems, networks, or data, this event belongs on your calendar.
Who Is Attending?
Black Hat USA draws thousands of cybersecurity professionals from around the world. Expect a mix of Fortune 500 security teams, government and defense personnel, academic researchers, and independent consultants. The Business Hall alone connects you with hundreds of solution providers and thousands of fellow practitioners.
The conference has historically attracted attendees from every major sector — finance, healthcare, technology, critical infrastructure, and government. The addition of Summit Day on Tuesday, August 4 adds a focused track for leadership-level discussions alongside the broader technical program.
Sponsors & Exhibitors
Black Hat USA 2026's Sustaining Partners represent the leading names in cybersecurity:
- Armis
- Cyera
- Google Cloud Security
- ManageEngine (Zoho Corp)
- Qualys
- SentinelOne
- Sophos
- Tenable
- ThreatLocker
- TrendAI
- Varonis
- Wiz
These sponsors anchor the Business Hall, which runs from Tuesday, August 4 through Thursday, August 6. Inside the hall, the Arsenal area hosts live demonstrations of open-source security tools, and the Bricks & Picks program returns with its hands-on physical security challenges.
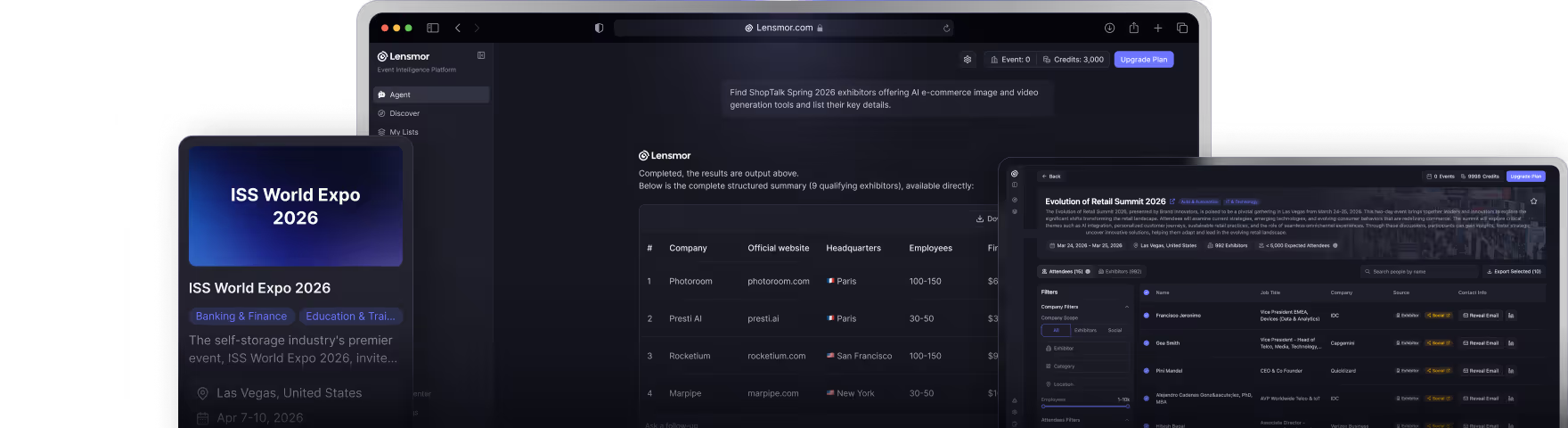
If you are preparing your team's conference strategy — tracking which events to attend, which vendors to meet, and how to divide your time — Lensmor can help you organize and prioritize across the full event schedule.
Speaker Lineup & Keynotes
Details to be announced. Check the official Black Hat website for updates.
The Briefings Review Board has been confirmed, which signals that the call for papers process is underway or complete. Past editions have featured keynotes from prominent security researchers, government officials, and industry leaders. Expect the full speaker lineup and keynote announcements to drop in the weeks leading up to the event.
Briefings will cover topics including:
- Applied security research
- Exploit development
- Malware analysis
- Cloud and infrastructure security
- Emerging threat landscapes
Full Agenda & Featured Events
Black Hat USA 2026 spans six days with distinct program tracks:
Trainings — Saturday, August 1 through Tuesday, August 4 Four days of intensive, hands-on courses led by world-class instructors. Topics range from ethical hacking and exploitation to malware reverse engineering and cloud security architecture.
Summit Day — Tuesday, August 4 A dedicated day of focused sessions running alongside the final day of Trainings and the opening of the Business Hall.
Business Hall — Tuesday, August 4 (afternoon) through Thursday, August 6 Hundreds of cybersecurity vendors, live product demos, the Arsenal open-source tool showcase, and the Bricks & Picks program. The Tuesday afternoon opening is new for 2026.
Briefings — Wednesday, August 5 & Thursday, August 6 Two days of peer-reviewed presentations covering the latest cybersecurity research, vulnerabilities, and defensive strategies.
On-Demand Access — Starting August 14 All recorded Briefings sessions become available on-demand beginning August 14, accessible for 30 days. This is valuable for anyone who cannot attend in person or wants to revisit sessions.
Registration & Ticket Pricing
Registration for Black Hat USA 2026 is available through the official Black Hat website.
Specific pricing tiers have not yet been published. Check the official Black Hat website for updates.
Historically, Black Hat USA offers several registration options:
- Briefings Pass — access to all Briefings sessions and the Business Hall
- Training Pass — enrollment in specific multi-day training courses (priced per course)
- Combined Passes — bundled access to both Trainings and Briefings
Early registration typically offers discounted rates. Group pricing may also be available for teams.
Frequently Asked Questions
When and where is Black Hat USA 2026?
Black Hat USA 2026 takes place August 1–6, 2026 at the Mandalay Bay Convention Center in Las Vegas, NV. Trainings run August 1–4, and Briefings run August 5–6.
What is new at Black Hat USA 2026?
The biggest change is the Business Hall opening on Tuesday afternoon instead of Wednesday. This gives attendees an additional half-day to network with vendors, explore the Arsenal, and participate in the Bricks & Picks program.
How much do Black Hat USA 2026 tickets cost?
Pricing has not yet been announced. Check the official Black Hat website for the latest registration details and early-bird deadlines.
Can I watch sessions after the event?
Yes. On-demand access to all recorded Briefings begins August 14, 2026 and remains available for 30 days. This does not apply to Trainings, which are live and hands-on only.
What is Black Hat Arsenal?
Arsenal is an open-source tool demonstration area located inside the Business Hall. Researchers and developers showcase security tools live, giving attendees the chance to see them in action and ask questions directly.
What other Black Hat events are happening in 2026?
Black Hat runs three major conferences each year:
- Black Hat Asia — April 21–24, 2026
- Black Hat USA — August 1–6, 2026
- Black Hat Europe — December 7–10, 2026
Additionally, DEF CON 34 traditionally follows Black Hat USA in Las Vegas and is worth considering if you are already in town.
Who reviews the Briefings and Trainings submissions?
The Briefings Review Board includes Lidia Giuliano, Jason Haddix, Window Snyder, and Anant Shrivastava. The Training Review Board includes Daniel Cuthbert, Ping Look, Maria Markstedter, and Jonathan Squire. These experts evaluate all submissions for technical rigor and relevance.