What Is DEF CON 34?
DEF CON 34 is the latest installment of one of the world's largest and longest-running underground hacking conferences. Scheduled for August 6–9, 2026, the event takes place at the Las Vegas Convention Center, West Hall, in Las Vegas, Nevada. DEF CON brings together thousands of security professionals, researchers, hackers, and technology enthusiasts for four days of presentations, workshops, demo labs, and specialized villages.
Since its founding in 1993, DEF CON has maintained a distinctive "hacker summer camp" atmosphere that sets it apart from corporate security conferences. The event operates at the intersection of cybersecurity, hacking culture, and technology policy. DEF CON 34 continues that tradition with a focus on community-based solutions, human interaction, and open-source tool development.
Whether you are a seasoned penetration tester or attending your first hacking conference, DEF CON 34 offers an unmatched environment for hands-on learning and direct engagement with the global security community.
Why You Should Attend
DEF CON 34 is not a passive conference. Attendees participate directly through capture-the-flag competitions, lock-picking workshops, hardware hacking labs, and village activities that reward curiosity and skill. The event prioritizes doing over watching.
The conference also serves as a proving ground for new vulnerability research and tool releases. Many critical disclosures and open-source security tools debut at DEF CON before reaching the broader industry. Attending gives you first access to cutting-edge research and the people behind it.
Beyond the technical content, DEF CON 34 offers networking opportunities that are difficult to replicate elsewhere. The informal atmosphere encourages genuine conversation between researchers, practitioners, and policymakers. You will leave with contacts, knowledge, and ideas that directly impact your work.
Key reasons to attend DEF CON 34:
- Hands-on learning through workshops, demo labs, and interactive villages
- First access to new vulnerability research and open-source tool releases
- Direct networking with thousands of security professionals and researchers worldwide
- Career development through skill-building contests and peer recognition
- Policy engagement with discussions on technology regulation and digital rights
Who Should Attend
DEF CON 34 draws a broad audience united by a shared interest in security and technology. The event is designed for participants across experience levels and professional backgrounds.
Ideal attendees include:
- Penetration testers and red teamers looking for new techniques and tools
- Security researchers preparing to present or discover new vulnerability disclosures
- Software and hardware engineers interested in the offensive security perspective
- IT and security managers evaluating emerging threats and defense strategies
- Students and career changers exploring cybersecurity as a profession
- Journalists and policy professionals covering technology regulation and digital rights
- Hobbyists and makers drawn to lock-picking, hardware hacking, and radio frequency experimentation
No formal credentials are required to attend. DEF CON has always valued skill and curiosity over titles
Full Agenda & Featured Events
[Section pending] — The confirmed agenda, village schedules, and featured events have not yet been announced. Check back closer to the event or visit defcon.org for updates.
While the full schedule is forthcoming, DEF CON 34 is expected to include:
- Villages — Focused communities covering topics like AI, car hacking, aerospace, IoT, social engineering, and more
- Capture the Flag (CTF) — Competitive hacking challenges for teams of all skill levels
- Demo Labs — Live demonstrations of new security tools and techniques
- Workshops — Instructor-led, hands-on training sessions with limited seating
- Contests — Lock-picking, scavenger hunts, badge challenges, and other community-driven competitions
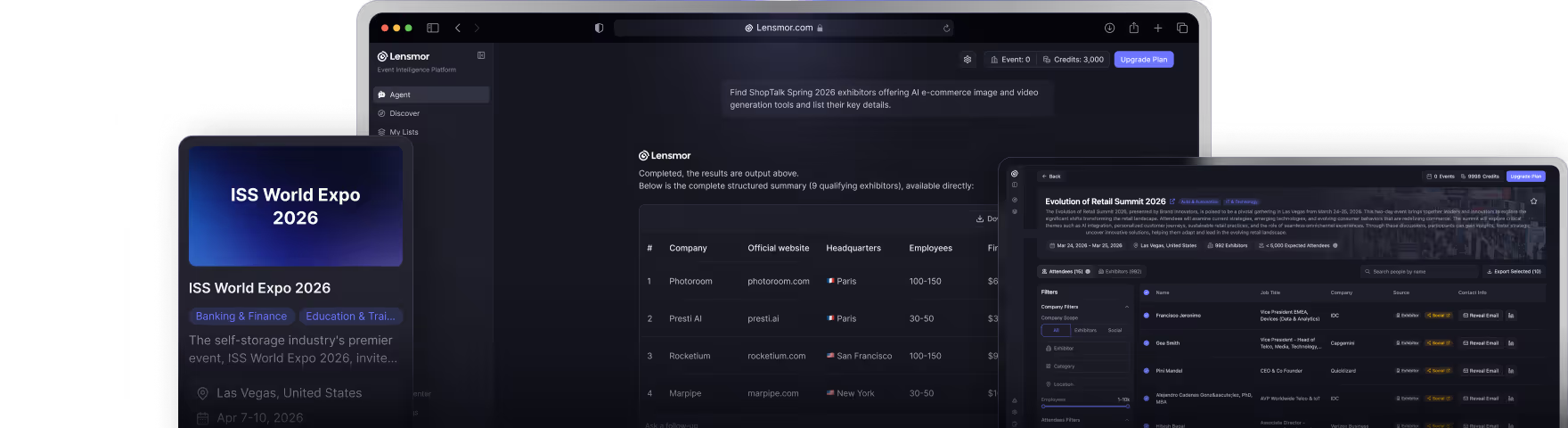
Plan to capture your DEF CON moments with Lensmor so you can revisit key sessions, village highlights, and networking connections long after the conference ends.
Registration & Ticket Pricing
Pre-registration for DEF CON 34 opened on March 4, 2026, with tickets priced at $520. Pre-registering guarantees you a physical badge — a custom-designed, collectible piece of hacker culture that serves as your entry pass.
For those who prefer the traditional walk-in experience, "LineCon" onsite registration is also available. Onsite registration is cash-only — no credit cards, no exceptions. This is a long-standing DEF CON tradition, so plan accordingly.
To pre-register for DEF CON 34:
- Visit the official DEF CON registration page at defcon.org
- Complete the pre-registration form and pay the $520 fee online
- Receive your confirmation and badge pickup instructions via email
- Pick up your physical badge onsite at the Las Vegas Convention Center, West Hall
For onsite "LineCon" registration:
- Bring cash only — $520 or the current onsite price
- Arrive early — the walk-in line can stretch for hours on opening day
- Receive your badge at the door and enter the conference
Frequently Asked Questions
Where is DEF CON 34 being held?
DEF CON 34 takes place at the Las Vegas Convention Center, West Hall in Las Vegas, Nevada. The West Hall is the convention center's newest expansion, offering modern facilities and ample space for the conference's many villages, workshops, and presentation tracks.
When does DEF CON 34 take place?
The conference runs from August 6 through August 9, 2026. Events typically start in the morning and run well into the evening, with unofficial gatherings extending into the night. Plan to arrive by August 5 to settle in before the conference begins.
How much do DEF CON 34 tickets cost?
Pre-registration is priced at $520 and guarantees a physical badge. Onsite "LineCon" walk-in registration is also available at the door for cash only. Pre-registering is recommended to lock in your spot and avoid long lines.
Is DEF CON 34 beginner-friendly?
Yes. While DEF CON attracts elite researchers and veteran hackers, many villages and workshops are specifically designed for beginners. The community culture encourages asking questions and learning by doing.
What should I bring to DEF CON 34?
- A dedicated laptop you do not mind exposing to a hostile network environment
- A burner phone or your primary device with a VPN configured
- Cash for onsite purchases, registration, and vendors
- A portable charger — long days drain batteries fast
- Comfortable shoes — the convention center is large and you will be on your feet
- A paper notebook for capturing ideas without connecting to the network
Is there a code of conduct at DEF CON 34?
Yes. DEF CON enforces a code of conduct that prohibits harassment, unauthorized recording in restricted areas, and illegal activity. Violations are taken seriously and can result in removal from the event.
Can I take photos and record sessions at DEF CON 34?
Policies vary by area. Always check posted signage and ask permission before recording anyone. DEF CON culture values privacy, and many attendees prefer not to be photographed. Respect those boundaries.
How do I stay updated on DEF CON 34 announcements?
- Visit the official website at defcon.org
- Follow DEF CON on social media for real-time announcements
- Join the DEF CON forums and community channels
- Subscribe to the DEF CON mailing list for email updates